To be clear, they factored a 22-bit RSA integer. this is impressive and noteworthy, but it doesn’t mean that RSA is fully broken yet as most RSA key-pairs are 2048 or 4096 bits.
Big caveat
Sure, it will be interesting to see how long it takes to scale up.
And currently the largest (publicly disclosed) quantum computer has 1,180 qbits.
Yes, but also it’s not looking good because theoretically this exploit could be applied over more bits with access to more qubits right? So it is only a matter of someone getting their hands on enough quantum computing cores.
But it was already theorized that this could happen, RSA had been considered unsuitable for a while now.
Exactly, this method scales with the size of the quantum computer, so we could see RSA broken within a decade. And this technique could apply to a lot of other existing algorithms. The key part to keep in mind is that there is a lot of encrypted data that has been collected already that people simply had no way to decrypt. So, there are retroactive consequences here as well.
Yeah, but RSA has been considered insecure for a while now because this attack was theorized.
Still, I’m sure there is a lot of RSA encryption out there through hardware keys and ssl certs and such…
Honestly? It really doesn’t matter that much considering the western empire basically owns the root-level chain of trust for nearly the entire internet. This is only for superpower state-level attacks, so why bother building a quantum supercomputers to crack RSA or break D-H, when you already have access to the private keys from nearly all CAs on earth? Not to mention almost no one uses anything resembling a secure OS or web browser, which is the only thing keeping your private keys secure.
Even if you’re shelling into a supersecret chinese personally-compiled openbsd VPS full of classified USDoD leaks, with your own personally managed 4096bit RSA keys with no other chain-of-trust to worry about, kicking down you door is going to be a hell of a lot cheaper and less complicated than building multi-trillion dollar gigantic secret underground quantum computers, that can, at best, break RSA in weeks instead of millennia. If that’s the case, then you better have strong disk encryption and nerves of steel. Ultimately breaking at-rest schemes and aes/(x)fish/serpent ciphers is more important.
If 4096bit RSA is somehow broken in our lifetimes, we can probably replace it with ed25519 or something more complicated and the arms race continues.
A large state breaking RSA is more-or-less a vanity project with regard to the implications.
Reading Chinese scientific advancements is truly joyful and uplifting in this often morbid world.
But at what cost?
I mean this one could actually be at a big cost. It would take a lot of effort to switch the world’s digital systems to be fully quantum secure, but this situation was inevitable either way.
There’s never going to be a such thing as quantum secure. Cryptography is an arms race. All we can really do is make the maths more complicated and take longer; all attackers can do is try to reduce the time it takes.
The best defence is always going to be being unknown.
As a matter of opsec, I mostly agree. But security is always best achieved in layers (and to a degree, redundancy). People running any CIA/NSA-backdoored operating system are compromised before even thinking about being discrete.
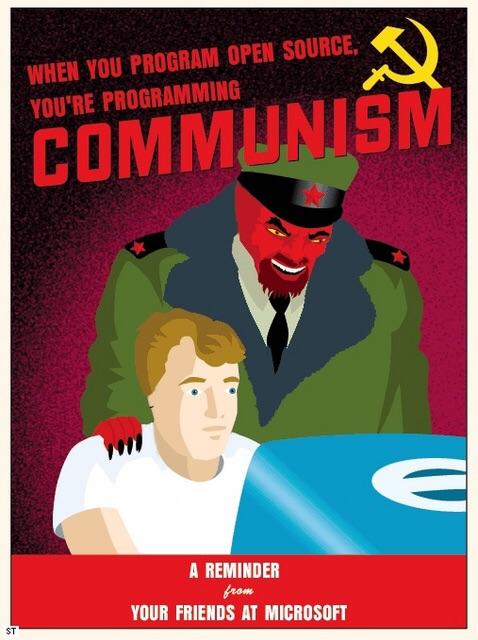
Always assume you will be surveilled. Always assume you will be caught. Ultimately it’s strong encryption and total rejection of closed-source software that gives you the best defense against the pigs.
deleted by creator
No, sorry, that’s just marketing bullshit for honeypots. There are no cosmic deep magic herbs and spices here. Just open encryption standards. But… Mullvad is based in Sweden, which is a member of the EU, NATO and 14-Eyes, however, which automatically makes the country (and every capitalist enterprise in it) part of the largest US-controlled mass surveillance programs on earth. It’s capitalism renting you the illusion of privacy while also purposefully destroying it.
deleted by creator
deleted by creator
Would this traffic be encrypted just because a website is https or do you have to do something else to encrypt it?
deleted by creator
Https is encrypted but it uses TLS which is a method thats pretty crackable with quantum computers as far as im aware
No. Current TLS ciphers and key exchanges, are EXTREMELY FAR from “pretty crackable” with anything, quantum or otherwise, especially when considering the lifetime of the keys are so short. The only entities we can reasonably foresee as capable of performing any kind of quantum cracking in the future are going to be global superpowers (arguably only the US and China).
But the keys to all TLS transactions are based in root CAs, and nearly all of those are subject to US/western intelligence jurisdiction. There’s no need for the state to crack RSA to compromise TLS. Look into how chain of trust works.
Because the traffics encrypted it cant be injected with malicious or otherwise stuff
MITM has been commercialized, it’s basically what Cloudflare does. If a host is behind CF your connection is only encrypted to CF, which then decrypts and re-encrypts the connection from itself to the host. Cloudflare is busy swallowing up the internet, so it’s not just state-level attacks that can openly compromise TLS with zero cracking required. VPNs can’t protect you from this, either.
The encryption is nice too but like i said it wont be secure for much longer so theyll have to update it soon to another protocol.
I’m sure you have good intentions, but you shouldn’t be making statements like this.
Thanks for explaining that.
deleted by creator