cross-posted from: https://sh.itjust.works/post/923025
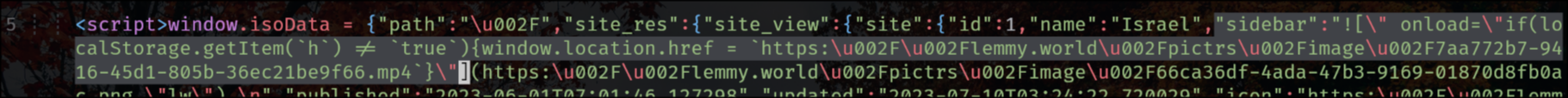
lemmy.world is a victim of an XSS attack right now and the hacker simply injected a JavaScript redirection into the sidebar.
It appears the Lemmy backend does not escape HTML in the main sidebar. Not sure if this is also true for community sidebars.
So the take-away so far is that lemmy.world including admin accounts may be compromised. XSS attacks are being used, perhaps in a targeted, perhaps generalized fashion to steal session cookies which is pretty bad as it allows the attacker to gain the login session of any victims. In the case of an admin they could do anything an admin could which is pretty bad as far as being able to steal user information, plant further malware, escalate the attack, etc.
Do not visit lemmy.world, be wary of any and all links you click.
Saw a claim on hexbear that the instance doing the attacks is zelensky dot zip which is definitely something though what I don’t know.
You should be able to invalidate any active login sessions by changing your password.
https://web.archive.org/web/20230710051744/http://zelensky.zip/
I had to use FireFox’s readability feature to even read the site. It’s like a ytmnd up in here.
Here is the raw text of and a link to an archive of zelensky dot zip.
Wish I knew more about code, I don’t really understand what this means. I did see that blahaj and potentially beehaw have been hacked too, little worried about us
deleted by creator
Elara said we should be safe, do you think she might be wrong?
Without going into specifics, yes.
I saw on Hexbear that XSS affected them as well. Do you know how an instance gets targeted by it? The post (on shitjustworks) that I read about it seemed to be related to code execution in the sidebar. So I thought the only way to do this would be if an admin modified the sidebar. But seems like this is not the case from what I read on Hexbear.
deleted by creator
well uh oh. Seems like we’re ok for now at least, maybe we should get the admins to shut the instance down
deleted by creator
her claim was that “Lemmygrad doesn’t allow HTML in its markdown parser”
deleted by creator
I don’t speak IT, can someone translate this for me?
deleted by creator
no clue either, elara said in the matrix that we should be safe because “lemmygrad doesn’t allow HTML in its markdown parser”
Looks like it’s time to install noscript (you can set global allowed mode and it still mostly kills most xss attacks). Meanwhile here I am sitting on top of default deny javascript for unknown non-whitelisted websites and laughing at pitiful attacks that don’t even target browser zero-days.
Is this a default Lemmy thing? Cuz someone on that original thread said that an admin account was used to create this vulnerability. I really hope that’s the case because protecting against XSS attacks is like, JavaScript 101.