

Shoutout to Frictional Games (known for Penumbra, Amnesia, Soma) who publish many of their older (commercially successfully) games on their GitHub: https://github.com/FrictionalGames


Shoutout to Frictional Games (known for Penumbra, Amnesia, Soma) who publish many of their older (commercially successfully) games on their GitHub: https://github.com/FrictionalGames


There is this notion that IPv6 exposes any host directly to the internet, which is not correct. When the client IP is attacked “directly” the attacker still talks to the router responsible for your network first and foremost.
While a misconfiguration on the router is possible, the same is possible on IPv4. In fact, it’s even a “feature” in many consumer routers called “DMZ host”, which exposes all ports to a single host. Which is obviously a security nightmare in both IPv4 and IPv6.
Just as CGNAT is a thing on IPv4, you can have as many firewalls behind one another as you want. Just because the target IP always is the same does not mean it suddenly is less secure than if the IP gets “NATted” 4 times between routers. It actually makes errors more likely because diagnosing and configuring is much harder in that environment.
Unless you’re aggressively rotating through your v6 address space, you’ve now given advertisers and data brokers a pretty accurate unique identifier of you. A much more prevalent “attack” vector.
That is what the privacy extension was created for, with it enabled it rotates IP addresses pretty regularily, there are much better ways to keep track of users than their IP addresses. Many implementations of the privacy extension still have lots of issues with times that are too long or with it not even enabled by default.
Hopefully that will get better when IPv6 becomes the default after the heat death of the universe.


Will take a look at the talk once I get time, thanks. If you can find the original one you were talking about, please link.
For servers, there is some truth that the address space does not provide much benefit since the addressing of them is predictable most of the time.
However, it is a huge win in security for private internet. Thanks to the privacy extension, those IPs are not just generated completely random, they also rotate regularily.
It should not be the sole source of security but it definitely adds to it if done right.


With NAT on IPv4 I set up port forwarding at my router. Where would I set up the IPv6 equivalent?
The same thing, except for the router translating 123.123.123.123 to 192.168.0.250 it will directly route abcd:abcd::beef to abcd:abcd::beef.
Assuming you have multiple hosts in your IPv6 network you can simply add “port forwardings” for each of them. Which is another advantage for IPv6, you can port forward the same port multiple times for each of your hosts.
I guess assumptions I have at the moment are that my router is a designated appliance for networking concerns and doing all the config there makes sense, and secondly any client device to be possibly misconfigured. Or worse, it was properly configured by me but then the OS vendor pushed an update and now it’s misconfigured again.
That still holds true, the router/firewall has absolute control over what goes in and out of the network on which ports and for which hosts. I would never expose a client directly to the internet, doesn’t matter if IPv4 or IPv6. Even servers are not directly exposed, they still go through firewalls.


Anything connected to an untrusted network should have a firewall, doesn’t matter if it’s IPv4 or IPv6.
There’s functionally no difference between NAT on IPv4 or directly allowing ports on IPv6, they both are deny by default and require explicit forwarding. Subnetting is also still a thing on IPv6.
If anything, IPv6 is more secure because it’s impossible to do a full network scan. My ISP assigned 4,722,366,482,869,645,213,696 addresses just to me. Good luck finding the used ones.
With IPv4 if you spin up a new service on a common port it usually gets detected within 24h nowadays.


I used to have a second partition with Windows for such cases, but over time I just stopped bothering with those games.
Now I just refund if it doesn’t work and move on in my to-play list.
I still have a Windows VM for some applications and for doing firmware updates but I never bothered to set it up for playing games.


I use ROCm for inference, both text generation via llama.cpp/LMStudio and image generation via ComfyUI.
Works pretty much perfectly on a 6900 XT. Very fast and easy to setup.
I had issues with some libraries only supporting CUDA when trying to train, but that was almost 6 months ago so things probably have improved in that area as well.


Is it safe to use JELLYFIN_SQLITE__disableSecondLevelCache all the time or should it only be used for testing?
I have had a lot of database lock issues since 10.9.


Yes, but it is the cause for having issues jumping between networks and never having proper IPv6 support.
What issues are you having? I have no issues with switching between networks and using IPv6 on Fedora KDE.
The only thing I ever noticed was that its stubborn with releasing its DHCP IP addresses and there is no refresh button in KDE. Disabling and enabling again usually solves that, although not sure if that is on NetworkManager or dhclient.
Everything is “out of scope” with GNOME these days it seems.
It is, that’s why it is not a suitable DE for people that need more than the basics. I wish they were better with adding advanced features but they are not and probably never will be.
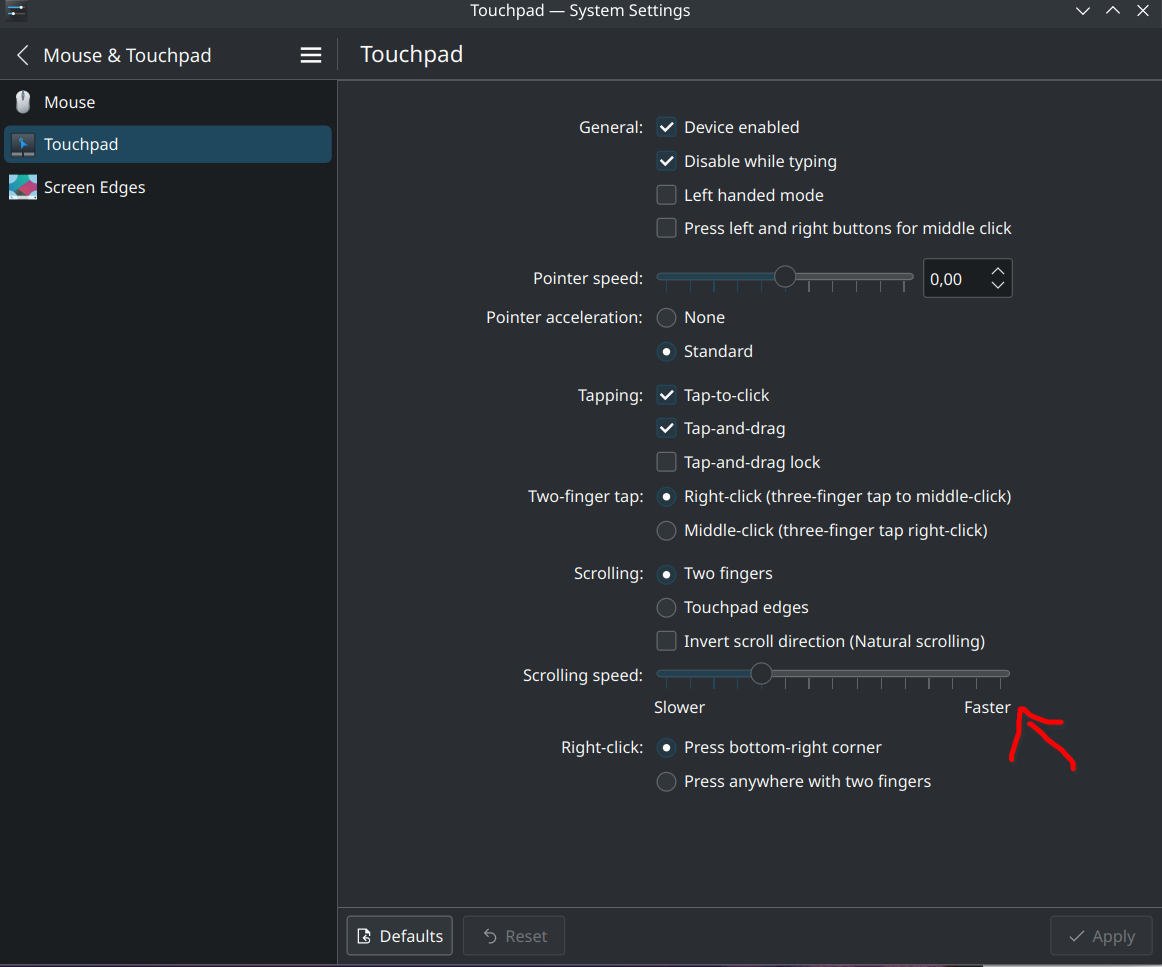
KDE might not be as pretty and flashy but it is pretty extensive when it comes to settings and fast with implementing new features.


NetworkManager is not the cause for having multiple UIs, that is just one of the side effects of GNOME going for the minimalistic approach. It’s never going to have all settings in their simple UI because that’s out of the scope for the GNOME project.
If having advanced network settings in a single UI is important to you, use KDE. It has wifi, static IPv4/IPv6, VLANs, routes, bridges, VPN and much more all in one interface.
Of course! If it has an installer, run it through Bottles first.
Once done, you can either start the game directly in Bottles or create a non-Steam shortcut in Steam and select the exe of the game you just installed.
I prefer running it through Steam because then I always have access to the latest Proton versions.
Didn’t try FF7 but played Alan Wake 2 like this.
That’s the reason I used the VLC alpha for a long time, it’s fixed there.
Moved away from VLC for music playback since then.


This seems like common sense, no?
Hindsight is 20/20. As seen in the post, there’s not that many APIs that don’t just blindly redirect HTTP to HTTPS since it’s sort of the default web server behaviour nowadays.
Probably a non-issue in most cases since the URLs are usually set by developers but of course mistakes happen and it absolutely makes sense to not redirect HTTP for APIs and even invalidate any token used over HTTP.
Make sure to let Bungie know that you want to play the game on your Steam Deck (even if you don’t have one) and it won’t launch for some reason.


Check out LM Studio. Very easy to get started and runs on both CPU and GPU.


Any source regarding “VR being usable” on linux?
I use VR with my Index almost every week on Linux. Filled to the brim with minor issues but definitely useable.
Still looking forward to a Deckard announcement, the Index is starting to show its age.


I run Fedora Kinoite on my work laptop and this is what the system settings look like. If GNOME can’t do that, then it indeed seems like a massive flaw.


I have been using this for a few hours now and it’s pretty great, so far my favorite of all the players I tried. Left the dev a few bucks on GitHub.


I’m aware of their reason for dropping support but it’s not sensible to drop a functioning system and replace it with nothing and then talk about how to do it better for years. That post is from 2017, it’s 2024 now and there is still no replacement in sight.
Yes, because Docker becomes significantly more powerful once every container has a different publicly addressable IP.
Altough IPv6 support in Docker is still lacking in some areas right now, so add that to the long list of IPv6 migration todos.